IBM 2025 Cost of a Data Breach: How AI and Shadow AI Shape Cybersecurity

The newly released IBM Cost of a Data Breach Report 2025 highlights how AI is reshaping the cybersecurity landscape, for better or worse.
These insights include the ups and downs in breach costs over the past few years, what is contributing to these fluctuations, the advancements in automation and AI security tools, and the associated risks of shadow AI. The findings serve as a wake-up call for enterprises that lack strong AI governance and unified security strategies.
Key Findings from the 2025 IBM Cost of a Data Breach Report
The new IBM report provides several compelling insights into how AI is impacting the cost and frequency of breaches:
Good news:
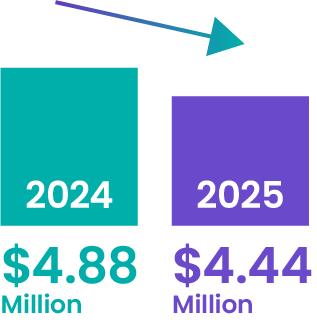
Global breach costs dropped from $4.88 million in 2024 to $4.44 million in 2025, returning to 2023 levels.
Faster identification and containment—thanks to AI, automation, and cybersecurity tools—are credited for this decrease.

Some bad news:
U.S. breach costs rose, hitting an average of $10.22 million, up from $9.36 million in 2024. The U.S. remains the costliest region for data breaches.
Shadow AI is a growing risk
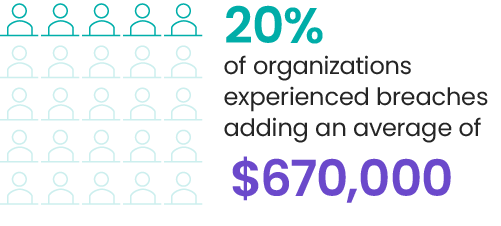
20% of organizations experienced breaches linked to unauthorized AI use, adding an average of $670,000 to breach costs.

AI governance gaps are widespread
63% of organizations surveyed have no AI governance plan or are still developing one.
AI-driven attacks are on the rise
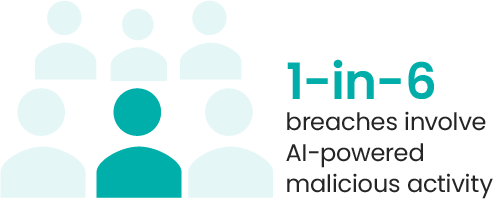
1-in-6 breaches involve some element of AI-powered malicious activity.
These findings underscore a paradox: while AI adoption has improved breach response and reduced average costs globally, the lack of proper oversight and governance creates new vulnerabilities that can rapidly escalate risk.
The Role of Aryaka Unified SASE as a Service in Addressing AI Risks
The new IBM report highlights a critical gap: AI is both a powerful tool and a potential threat. Without proper visibility and governance, organizations face rising risks from shadow AI and sophisticated AI-driven attacks. Aryaka Unified SASE as a Service directly addresses these challenges by delivering converged networking and security capabilities on our global Zero Trust WAN. Powered by our OnePASS Architecture, Aryaka enforces consistent security policies and provides complete visibility across every connection—HQs, branch offices, cloud workloads, and remote users.
With this unified approach, Aryaka enables enterprises to detect, control, and mitigate risks associated with unauthorized AI usage while maintaining high-performance, secure access for legitimate workloads.
How Aryaka CASB Protects Against Shadow AI
A major insight from the IBM report is the costly impact of shadow AI—unauthorized or unmanaged AI tools used by employees or departments without IT oversight.
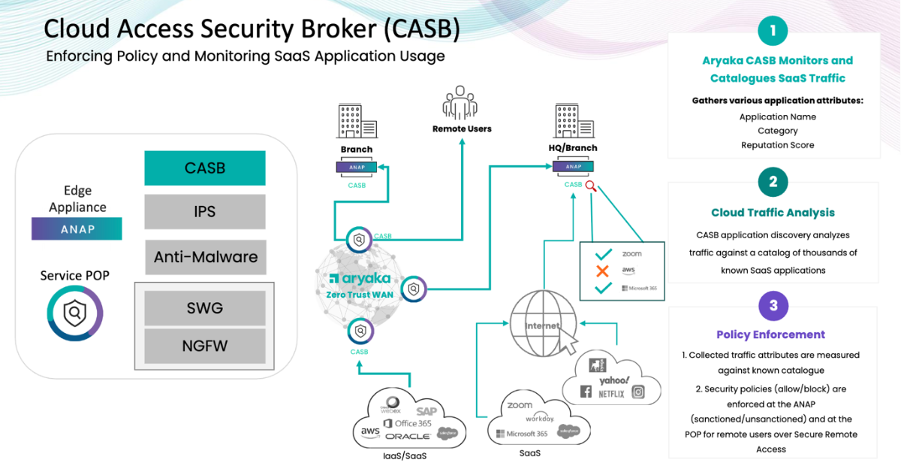
Aryaka’s Cloud Access Security Broker (CASB) is purpose-built to address this challenge by:
- Identifying AI and SaaS application traffic across the global network mesh as they pass through our ANAPs and POPs.
- Measuring usage patterns to assess risk levels and detect anomalies.
- Categorizing AI applications, distinguishing between sanctioned and unsanctioned tools.
- Enforcing Policies in real time to block risky AI usage, prevent data exfiltration, and ensure compliance with governance frameworks.
By delivering CASB as part of a unified SASE service, Aryaka ensures that AI traffic is monitored and controlled without adding complexity or blind spots.
Aryaka AI>Observe: Harnessing AI to Strengthen Security
The IBM report also shows that AI is not only part of the problem but also part of the solution. Aryaka AI>Observe embraces AI to enhance threat detection, telemetry analysis, and incident response across the entire network.

Leveraging AI learning and advanced analytics, AI>Observe:
- Provides real-time visibility into security events across HQs, branches, cloud, and remote endpoints.
- Correlates telemetry to detect patterns that indicate potential breaches or malicious activity.
- Reduces response times by highlighting high-priority incidents and automating key workflows.
- Enhances overall network observability, enabling security teams to stay ahead of evolving threats—including AI-driven attacks.
By combining AI-driven observability with unified enforcement, Aryaka equips enterprises to close the oversight gap identified in the IBM report.
Final Thoughts
The IBM 2025 Cost of a Data Breach Report reveals two clear truths: AI can dramatically lower breach costs when leveraged responsibly, but without strong oversight, it becomes a new attack surface. Shadow AI and AI-powered threats are already driving up breach costs for organizations lacking governance.
Aryaka Unified SASE as a Service provides the visibility, control, and AI-powered insights needed to defend against these emerging risks. With integrated CASB to govern AI usage and AI>Observe to strengthen detection and response, Aryaka enables enterprises to harness the benefits of AI while mitigating its dangers.
Learn more about how Aryaka converges your networking and security

