Securing the Data – SASE, CNAPP and CSMA roles

Data has become the most valuable resource for Enterprises. No wonder, there are many bad actors trying to disrupt the Enterprise businesses from stealing & corrupting the data.
Data security is all about protecting the data from unauthorized users, corruption of data with malicious intent and data theft. You may wonder why many security companies talk about protecting the applications, networks, endpoints, but less about data. The reason is that there is a strong relation between data and applications & systems. Unless applications & systems are protected from bad actors, data security is not possible.
‘Data is the new Oil’ phrase explains the relationship between applications & data. Data just like oil in its raw form is not useful unless it is refined for consumption. Applications work on data and present it to the users in easy-to-consume fashion.
SASE role in Data Security
Please read Deciphering SASE blog for an overview of SASE.
SASE plays an important role in protecting the applications in this world of distributed workforce and distributed deployments across On-Prem Cloud, public cloud, and public edges. Following sections provide some of the key security concerns and how SASE addresses them.
Enterprises develop or deploy many applications for various business purposes. All applications may not require accessing all the Enterprise data. And all users of the applications don’t need access to all the application data. Due to this, “Least Privilege Access” & “Identity based Access Controls” are the key to data security.
Applications are not simple anymore. Developers use many software components – in house built, purchased and open source – making the software complex and more vulnerable. Attackers tend to leverage the threat knowledge base and try exploiting the vulnerabilities to get access to the applications and then to the data. Hence, threat protection from exploits is important for data security.
Application & system administration is most critical as the application administrators tend to have higher privileges. Any credential stealing of admin accounts can be havoc for Enterprises. Few security techniques such as adopting a second level of MFA, restricting users accessing from unsafe / unknown locations, restricting users exhibiting abnormal behavior patterns are needed for added data protection.
Enterprises deploy applications in many locations to provide low-latency user experience to the distributed workforce and to ensure that applications can withstand increased or abnormal load. With distributed applications, data is also distributed. Due to this, security is also expected to be distributed to address increase in demand & DDoS attacks on applications.
ZTNA (Zero Trust Network Access) platform and NGFW (Next Generation Firewall) of SASE addresses above security concerns. Due to this, SASE is becoming one of the key cybersecurity elements addressing data security via protecting applications as well as enabling identity-based access & authorization controls.
One might ask ‘Are ZTNA & NGFW good enough’ for securing the applications and thereby securing the data. With Cloud transformation of leveraging public clouds, public edges for Enterprise applications, there are more attack surfaces. Data security requires fixing those attack surfaces. That is where CNAPP comes into picture.
Increased attack surface with Cloud transformation
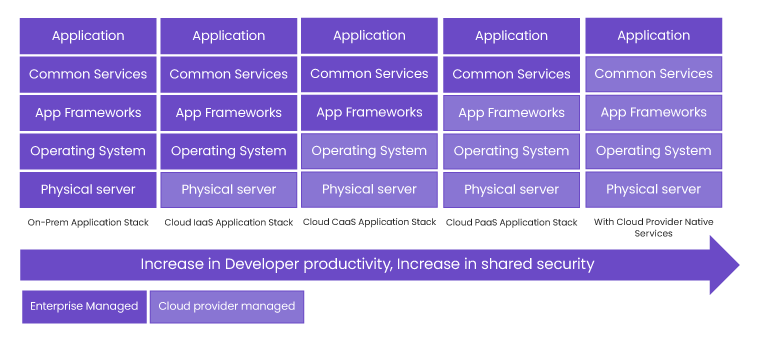
Cloud transformation of simpler applications reduces the Enterprises responses as security for the common infrastructure software is taken care of by the cloud providers. From this picture, applications’ developers are increasingly focusing on the business logic and leaving the mundane software components’ responsibility to cloud providers.
It is true that developers only need to focus on application logic and leave the maintenance and security patching of operating systems, frameworks, common services such as databases, file storage, key management, authentication, authorization systems and observability systems to cloud providers, thereby reducing security responsibilities limited to the applications
That said, distributed workforce and new kinds of applications requiring low latency experience are complicating the application deployments and thereby exposing more attack surfaces.
Applications are increasingly needed to be deployed on multiple locations not only across regions of a cloud provider, but also across multiple cloud providers and edge providers to provide best user experience. In addition, applications are increasingly deployed in Edges on demand basis. That is, applications are deployed only when there are clients in the vicinity that require application services. Deploying the full complex application across all Edges is not warranted for cost reasons. Welcome to microservice architecture. Application developers are adopting microservice architecture not only for higher productivity, but also to enable partial application deployment in Edges and keep the rest in the clouds.
Following picture (made it simple for brevity) shows the microservices based application deployment. In this arbitrary application example, Microservice 1 and 2 of the application are deployed in the Edges to provide low latency experience and Microservice 3 and 4 are deployed in the clouds for other operations of the application. There are 5 attack surface points shown in the picture.
- Communication between end clients and frontend microservice 1 and inter microservice communication across Edges & Cloud
- Communication among microservices within edge locations or cloud locations.
- Communication between application microservices and cloud/edge provider services
- Communication with provider services from outside to provider services.
- Internal software components of microservices

Any comprehensive security is expected to address all attack surfaces.
Attack surfaces (1) can be addressed by SASE ZTNA & NGFW. All other attack surfaces came to the light due to distributed computing, microservice architecture and applications using cloud provider services. Since this is mostly due to cloud/edge transformation, Gartner defined a new category called CNAPP model to address these security challenges.
CNAPP (Cloud Native Application Protection Platform) to address increased attack surface
CNAPP is a cloud native security model/technology that combines Cloud Security Posture Management (CSPM), Cloud Service Network Security (CSNS) and Cloud Workload Protection Platform (CWPP) in a single platform. By combining multiple cloud security tools into one platform, CNAPP provides benefits such as comprehensive visibility across application life cycle – build, deploy to runtime phases, and comprehensive controls across multiple technologies. Just like other terms coined by Gartner, CNAPP term is also expected to provide common understanding of security function/platform capabilities between suppliers and consumers. Let us check what CNAPP constitutes and then map attack surface points to these constituents.
Cloud Security Posture Management (CSPM): CSPM capability gives Enterprises the visibility of all the cloud resources/services Enterprise applications use from multiple cloud providers. CSPM also maps the cloud services and applications that use them.
Biggest benefit of CSPMs is configuration scanning to detect any misconfigurations. Since cloud provider services are very generic, its security is as good as its configuration. It is important to understand that the cloud provider services are multi-tenant, and their access can’t be controlled by Enterprises. If they are misconfigured, attackers can get to those services and steal & corrupt the data. For example, if a database service is configured to allow access from anybody by mistake, it can give away the Enterprise data stored by applications in the database service.
CSPMs also perform compliance checks on the data in cloud services and provide compliance violation visibility to Enterprises.
CSPMs address attack surface (4) listed in the above picture.
Cloud Service Network Security (CSNS): CSNS provides network level security among the microservices of the applications as well as the network security between microservices and cloud services. Its functionality is like SASE/ZTNA. Its functionality includes NGFW, WAF, Identity based access control, WAF, API protection, DoS/DDoS prevention. CSNS differs in its dynamism from traditional network security. Due to dynamic workloads, CSNS security life cycle needs to be inline with the life cycle of applications.
CSNS addresses attack surface (2) and (3) in the above picture. Essentially CSNS provides network security for E-W traffic.
Cloud Workload Protection Platform (CWPP): CWPP function predominantly checks for
- Vulnerabilities in the workload images (VM, Container, Serverless) by analyzing the images, getting hold of software inventory, inventory versions and checking with threat intelligence databases to understand any known vulnerabilities in the software inventory.
- Malware detection and unwanted software detection in the images to ensure that no malware was introduced in its supply chain.
- Exploits at run time via Host Intrusion Prevention technology.
- Runtime memory protection using secure guard technologies such as Intel SGx.
- Runtime workload protection via RASP (Runtime Application Self Protection)
CWPP addresses attack surface (5) listed in the above picture.
With the popularity of Kubernetes for applications, above technologies are delivered to work on Kubernetes. KSPM (Kubernetes Security Posture Management) is similar to CSPM but tuned for Kubernetes. It may be a matter of time, one would see the terms such as KWPP (Kubernetes Workload Protection Platform) and KSNS (Kubernetes Network Security Service).
CSNS and SASE
CSNS functionality looks a lot like ZTNA & NGFW. That is because both are network security technologies. Enterprises like to see uniform technology for both N-S (North-South) and E-W (East-West) traffic. Hence, the belief is that CSNS functions would be delivered by SASE providers. Universal SASE is expected to address all network related attack surfaces, whether they are WAN, Kubernetes networks, Kubernetes networks with service mesh, VPC networks, Edge networks etc. This seems to be the trend and accepted as many CNAPP providers don’t talk much about CSNS anymore.
Cyber Security Mesh Architecture (CSMA)
One of the biggest challenges Enterprises face is security silos. Enterprises are used to deploy multiple security functions from various vendors to address On-Prem Security, Endpoint security, Network Security, Cloud security requirements. Each security function comes with their policy management, observability, and data plane. As a result, management and visibility becomes complex leading to security configuration errors and thereby missed or delayed security incident detections and responses. Gartner created the CSMA term as part of their security thought leadership. Gartner recognized that Enterprises would need to go for multiple security functions from various security vendors. CSMA concept is trying to address the needs of Enterprises that require single-pane-of-glass for policy management & observability.
Gartner defined some principles to be followed by security vendors to enable composition of multiple security functions. Predominant principle being the API exposure by security vendors over and beyond CLI and Portal interfaces. API-first approach allows Enterprises or managed security providers to realize a single consolidated dashboard for policy management and security analytics.
Gartner also points out the need for ‘identity fabric’ with decentralized identity of users. Today, Enterprises maintain the credential database using technologies such as AD, LDAP, SAML IdPs and OIDC IdPs etc. Even though it is okay to have a database of identities of employees, maintaining an ID database for public users is a challenge from privacy & security aspects. Offloading identity database & identity checks to distributed identity providers is a win-win for both Enterprises and end users. ADI Association and W3C are working on a common framework and specifications to realize decentralized identity fabric.
Though CSMA does not directly address actual security, this architecture/concept minimizes the security configuration errors and provides E2E visibility for faster incident detection and response.
SASE and CNAPP are right in the direction towards realizing CSMA. SASE consolidates all network security functions and network functions by providing single-pane-of-glass for network security policy management & observability. CNAPP consolidates all cloud security functions under one umbrella. CSMA is one level higher consolidation encompassing SASE, CNAPP, Endpoint security, identity, and other cybersecurity technologies.
Summary
Data security requires many technologies such as Data encryption, Data governance, Data masking and Cybersecurity. SASE is an integral part of Cybersecurity. Cloud and Edge transformation coupled with newer application architectures such as Microservice architecture exposes additional attack surface points. CNAPP, coupled with Universal SASE addresses the security challenges associated with new attack surfaces.
-
CTO Insights blog
The Aryaka CTO Insights blog series provides thought leadership for network, security, and SASE topics. For Aryaka product specifications refer to Aryaka Datasheets.
- Cutting Through the SASE Confusion
- Enterprise Networks at an Inflection Point: The Motivations for SASE
- Managed Multi-Cloud Connectivity and SASE
- Demystifying SASE Adoption
- Fully Managed SASE for Better TCO – Check Point & Aryaka
- Re-Defining Hybrid Workplace with SASE and a Cloud-First Solution
- Re-Defining VPN with SASE and a Cloud-First Solution
- Which SASE is right for you?