Network Visibility Solutions: Seeing Is Believing

It was just another day on April 3rd, when suddenly cybersecurity professional Alon Gal’s twitter handle started trending. News of a massive Facebook data breach — leaking details of more than half a billion Facebook users from 106 countries — had hit the headlines. It quickly came to light that this was not a new data breach, but an old one that had come back from the grave to haunt Facebook, releasing user phone numbers and IDs. An almost textbook illustration of the security flaws that still prevail in many critical infrastructures.
A recent study by ZK Research suggests that 90% of mean Time-to-Resolution (TTR) goes into identifying the problem. My point — Security and visibility are not mutually exclusive. For the better part of last two decades, the ability to instantly locate the status of different moving parts in the enterprise IT infrastructure has been one of the holy grails for network security. Millions of dollars have been vested in building feature sets that help businesses get a clear vantage point into the entire end-to-end infrastructure.
So how does the network piece tie into all of this?
The Bar of Success Is a Moving Target
Let me put it this way — Of all the technologies that have changed our lives, the internet (a subset of network connectivity) perhaps has had the most profound effect on us. In retrospect, the internet changed us, and in turn we changed the internet. It has gone from playing Pac-Man to powering scalpel-wielding robots in real operations.
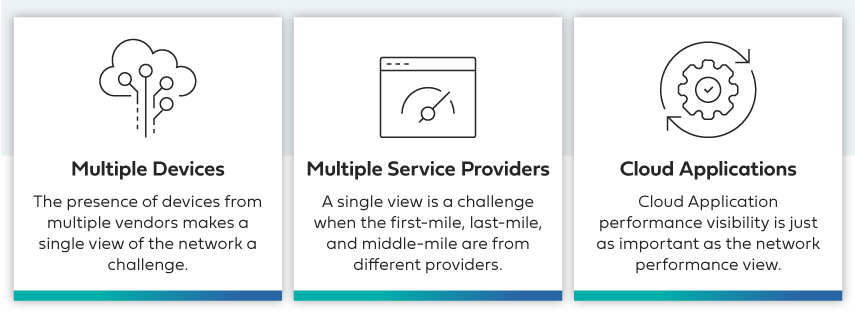
Here are the top three factors that add to the complexity.
Rising Network Sprawl
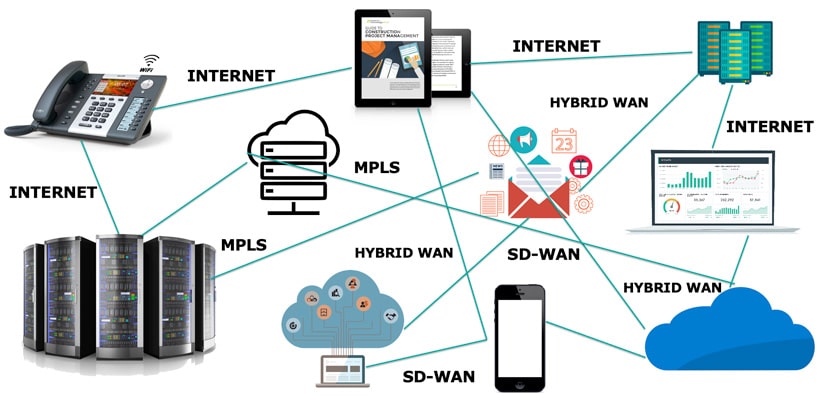
Blame it on the proliferation of network-aware devices, rise of the cloud, unified communications, or demise of the on-premises culture — the enterprise network infrastructure is doing more heavy lifting than ever before.
You’ve got multiple links spun-up globally across distributed data centers, span ports, network packet brokers, servers, and network taps. You have the WAN connecting branches to the cloud, the cloud to data centers, data centers to remote locations, data centers to data centers, and everything else in between. Complete network visibility, sometimes called observability, helps you decide what works, what does not work, and what needs to be upgraded to optimize the infrastructure.
The Cloud Is a Complex Beast
What was once known for its simplicity has evolved into a multi-headed beast. Hybrid cloud, multi-cloud, internal cloud systems, and the rising fusion of enterprise data centers with cloud services — the menu for cloud services keeps growing.
Active communication between multi-clouds and data centers dramatically increases the network traffic. Moreover, when you glue together multiple resources to run your mission-critical applications, network monitoring becomes imperative to understand the infrastructural interdependencies, detect security issues, and improve maneuvering. In fact, the network becomes more critical because these functions are no longer running in an on-premises environment, commonly assumed to be a more controlled environment.
Growing Number of Applications
Application complexity keeps compounding every year. Some stay on-premises, some move to the cloud, and some reside in-between. Most of these applications are delivered over a network and are highly distributed. Hence the network medium needs to be congestion-free. More importantly, being mission-critical, each second of downtime translates into lost revenue.
Allow me to translate — If connection to a specific data center is lost, your IT team should have enough insight to route the traffic to another data center, steering away from any potential service downtime. That’s precisely why visibility across these applications, and the network they are being delivered upon, is so important. Any potential blind-spots can be fatal.
To Each His Own!
Let’s see how different SD-WAN models approach the visibility equation.
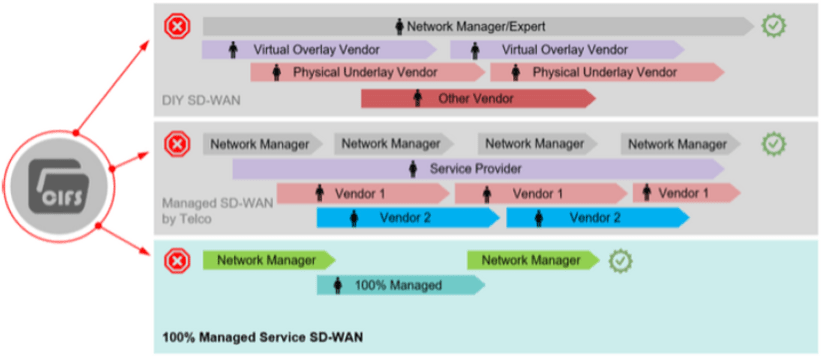
DIY SD-WAN
Say your application is behaving unusual and you choose to save the day yourself. Now it’s up to you and your network expert. After much diagnosis the network piece seemed fine, and you went ahead with the application part. Here you are met with the physical underlay and the virtual overlay. The chances of detecting the anomalies with in-house expertise and monitoring tools are very slim — if not zero. Follow up steps? Coordinate with the applications support, run between multiple vendors, contact the MPLS provider and / or ISP, and pay hefty support charges.
Managed SD-WAN by the Telcos
Nothing much changes. You just added a layer of a service provider in-between. Wait till you find out that the service providers barely have any expertise pertaining to the virtual overlay solution. In the event of a crisis, they will end up ringing the overlay folks—something you would have done anyway.
Now, to the physical underlay. Apart from a handful of providers, namely AT&T or Verizon, no service provider has a truly global footprint. The majority work with disparate vendors with little to no expertise with the local ISPs, and with stark cultural and performance variations in different regions of the world. If things go south, they will call the service providers and ISPs and do precisely what you would’ve done. So, all you did was add a layer and obfuscate the real problem.
A Fully-Managed Cloud-First WAN
Here you have a visibility solution that lets you see the underlay, the overlay, facilitates application performance monitoring, with an eagle-eye view of the entire infrastructure, and dedicated network performance monitoring and security tools in the remotest of sites.
When Murphy’s law strikes and things go sideways, you just have to ring the experts and let them do what they do best. No patchy vendor infrastructure managed via. partnering relationships. Sounds like a complete package to me.
In Conclusion
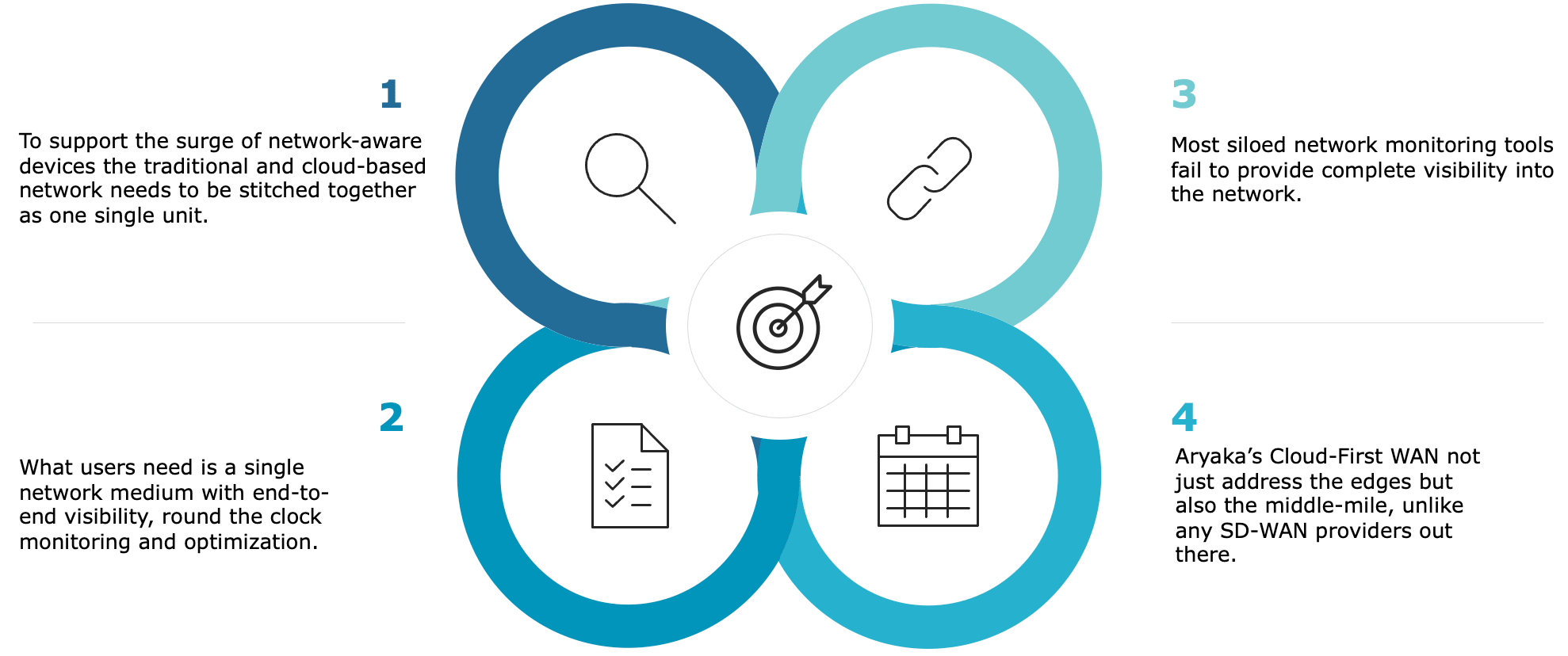
Aryaka is in a unique position to help these enterprises. Our solution not only address the edge but also the middle-mile, unlike most other SD-WAN providers. This empowers your network admins to have end-to-end visibility into anything and everything riding the network, along with the ability to configure, control and manage Aryaka’s Solutions. The built-in intelligence ensures that the networks are set up, configured and remain optimized at scale in an increasingly distributed IT environment.
Want to know what your industry peers and leaders are thinking? Download the latest State of the WAN Report that has insights gleaned from 1,350 network and IT practitioners at global enterprises in various industries and across all regions.
Already read enough? Watch State of the WAN webinar.
Want to see if we can walk the talk on our network monitoring claims? Book an SD-WAN demo.
- Accelerate CAD/CAM Performance
- Improve Zoom Conferencing Performance
- Calypso Embraces a SaaS-first Strategy
- CallisonRTKL Transforms their WAN
- Kleinfelder Improves Application Performance
- Teradyne Transforms their WAN
- SAP web application performance
- Kleinfelder Improves Application Performance
- Industrial Manufacturing Company Transforms WAN